Friday, May 22, 2020
How Block Chain Technology Can Help Fight Wuhan Corona Virus Outbreak
As the death toll and the infected cases of widespread coronavirus continue to increase, global organizations and the tech industry has come forward with technology like blockchain to fight coronavirus.
Along with the equipment and monetary support, technology also withstands against the virus with better plans and solutions. Hence, tech industries have started leveraging blockchain technology in the wake of a global health emergency.
Blockchain Helps In Real-Time Online Tracking
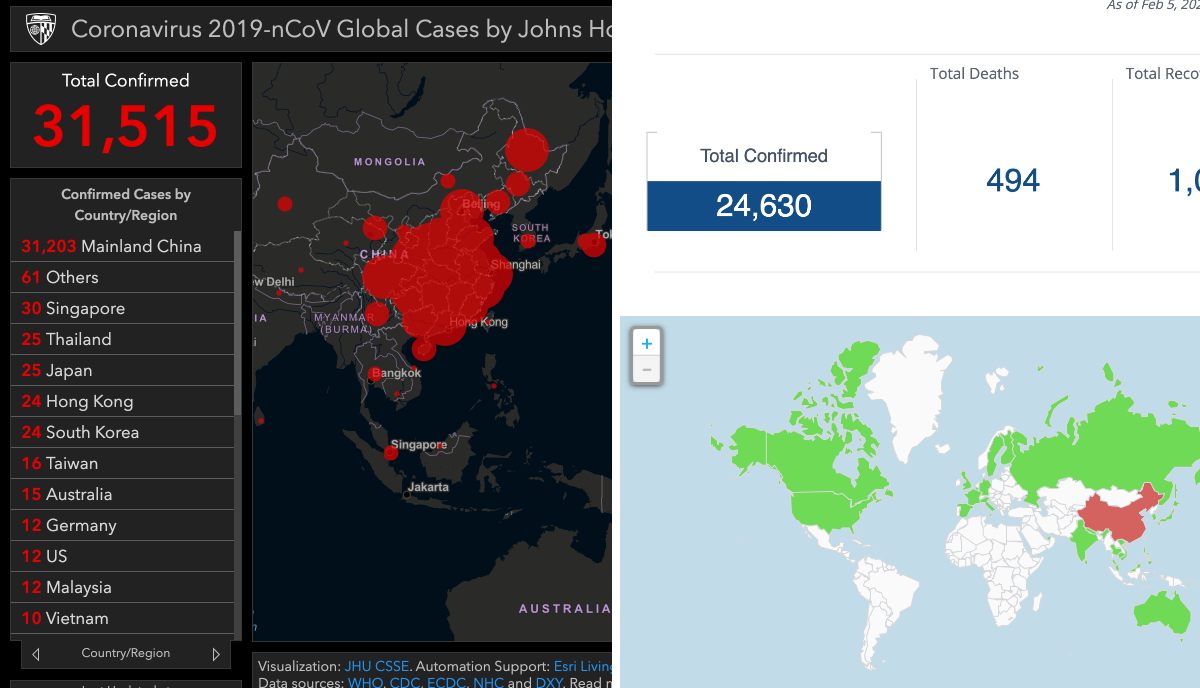
The Center for Systems Science and Engineering has already set up an online platform to track coronavirus and visualize the growing number of infected patients in real-time.
But Acoer, an Atlanta-based blockchain app developer, has also launched an alternative online data visualization tool to easily trail and depict the Cororanvirus outbreak using blockchain technology.
Acoer platform, named HashLog, is more advanced and clear as it pulls the data from the Hedera Hashgraph database using the HashLog data visualization engine.
Hedera Hashgraph is an immutable, transparent and decentralized database based on distributed ledger technology that provides synchronized and unchangeable data from the public networks.
Moreover, researchers, scientists, and journalists can use the HashLog dashboard to understand the spread of the virus and act against it swiftly.
For data sources, Johns Hopkins CSSE extracts data from WHO, CDC, ECDC, NHC, and DXY. On the other hand, Acoer maps the public data, including data from the Center for Disease Control (CDC) and the World Health Organization (WHO). Therefore, data may differ on both platforms.
Blockchain Can Help Monitor And Control Money Flow
To fight the further spread of the coronavirus (2019-nCoV) outbreak globally, China has also received abundant monetary support from the international community to create better action plans.
China's govt-led organization and charities are responsible for overseeing and utilizing the influx of money to research and generate a solution for coronavirus. But due to the lack of coordination and mismanagement among the various organization, money is not being laid out to curb the crisis.
Recently, a paper published by Syren Johnstone, from the University of Hong Kong, discusses the problems encountered by charities, in China and elsewhere. It argues that the present crisis should be seen as a call to arms.
Syren urges for a borderless solution with better management of donations and implementation using the emerging tech like Blockchain and Artificial Intelligence.
Keeping that in mind, Hyperchain, a Chinese company, also announced blockchain-based charity platform to streamline the donation from all over the world.
Since the Hyperchain platform is based on the blockchain, it offers more transparency among the sender and receiver of funds to bring trust and immutability to restrict the transaction data deletion.
Overall, Hyperchain improves administrative function for the money and also extends the logistics actions.
@HACKER NT
More info- Capture The Flag Hacking
- Que Hace Un Hacker
- Tecnicas De Ingenieria Social
- Hacking Simulator
- Hacking Tor Whatsapp
- Growth Hacking Marketing
- Google Hacking Database
- Curso De Ciberseguridad Y Hacking Ético
The RastaLabs Experience
Introduction
My experience
RastaLabs starts in 3,2,1 ...
Lateral movement
About exploitation
Conclusion
Footnote
OSCP has no power here. Cry harder!
Related articles
Thursday, May 21, 2020
Contratar Hackers Profesionales Para Hackear WhatsApp, La Universidad Y Espiar A Tu Pareja: La Estafa.
 |
| Figura 1: Contratar hackers profesionales para hackear WhatsApp, la universidad y espiar a tu pareja: La estafa. |
 |
| Figura 3: Página de Hackers Profesionales for Hire |
 |
| Figura 4: Servicios de Hackers |
 |
| Figura 5: "Buscas contactar un Hacker Informatico en Barcelona" o en Madrid |
 |
| Figura 6: Algunas cosas en las que somos geniales!! |
 |
| Figura 7: "Metodo hackear Whatsapp" |
 |
| Figura 9: Servicios Hacker Profesional |
 |
| Figura 10: "No confíe en nuestra palabra: esto es lo que dicen nuestros clientes" |
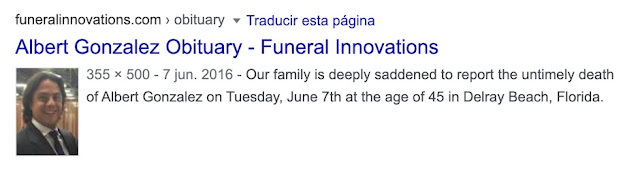 |
| Figura 11: Uno de los supuestos clientes es una persona fallecida |
 |
| Figura 12: El supuesto equipo de "Hackers Profesionales" |
 |
| Figura 13: Andrés Ferrari es un modelo de barbas |
 |
| Figura 14: Supuesto exploit usado |
 |
| Figura 16: Cómo protegerse de los peligros en Internet de José Carlos Gallego Cano |
Related articles
- Brain Hacking
- Como Convertirse En Hacker
- Master Growth Hacking
- Hacking Gif
- Certificacion Hacking Etico
- Hacker Significado
- Cracker Informatico
- Raspberry Pi Hacking
- Hacking Software
- Hacking Language
What Is Cybersecurity And Thier types?Which Skills Required To Become A Top Cybersecurity Expert ?
The term cyber security refers to the technologies and processes designed to defend computer system, software, networks & user data from unauthorized access, also from threats distributed through the internet by cybercriminals,terrorist groups of hacker.
More information
- Hacking Tutorials
- Hacking Etico Pdf
- Tools Hacking
- Bluetooth Hacking
- Hacking Wifi Android
- Linux Hacking Distro
- Hacker En Español
- Hacker Definicion Informatica
- Brain Hacking
Reversing Pascal String Object
The program:
program strtest;
var
cstr: array[0..10] of char;
s, s2: ShortString;
begin
cstr := 'hello world';
s := cstr;
s2 := 'test';
WriteLn(cstr + ' ' + s + ' ' + s2);
end.
We are going to compile it with freepascal and lazarus, and just the binary size differs a lot:
lazarus 242,176 btytes 845 functions
freepascal 32,256 bytes 233 functions
turbopascal 2,928 bytes 80 functions (wow)
And surprisingly turbopascal binaries are extremely light.
Lets start with lazarus:
On functions 10000e8e0 there is the function that calls the main function.
I named execute_param2 because the second param is a function pointer that is gonna be executed without parameters, it sounds like main calling typical strategy.
And here we are, it's clearly the user code pascal main function.
What it seems is that function 100001800 returns an string object, then is called its constructor to initialize the string, then the string is passed to other functions that prints it to the screen.
This function executes the method 0x1c0 of the object until the byte 0x89 is a null byte.
What the hell is doing here?
First of all let's create the function main:
After a bit of work on Ghidra here we have the main:
Note that the struct member so high like 0x1b0 are not created by default, we should import a .h file with an struct or class definition, and locate the constructor just on that position.
The mysterious function was printing byte a byte until null byte, the algorithm the compiler implemented in asm is not as optimized as turbopascal's.
In Windbg we can see the string object in eax after being created but before being initialized:

Just before executing the print function, the RCX parameter is the string object and it still identical:
Let's see the constructor code.
The constructor address can be guessed on static walking the reverse-cross-references to main, but I located it in debugging it in dynamic analysis.
The constructor reads only a pointer stored on the string object on the position 0x98.
And we have that the pointer at 0x98 is compared with the address of the literal, so now we know that this pointer points to the string.
The sentence *string_x98 = literal confirms it, and there is not memory copy, it only points reusing the literal.
Freepascal
The starting labyrinth is bigger than Lazarus so I had to begin the maze from the end, searching the string "hello world" and then finding the string references:There are two ways to follow the references in Ghidra, one is [ctrl] + [shift] + F but there is other trick which is simply clicking the green references texts on the disassembly.
At the beginning I doubted and put the name possible_main, but it's clearly the pascal user code main function.
The char array initialization Is converted by freepascal compiler to an runtime initialization using mov instructions.
Reducing the coverage on dynamic we arrive to the writeln function:
EAX helds a pointer to a struct, and the member 0x24 performs the printing. In this cases the function can be tracked easily in dynamic executing the sample.
And lands at 0x004059b0 where we see the WriteFile, the stdout descriptor, the text and the size supplied by parameter.
there is an interesting logic of what happens if WriteFile() couldn't write all the bytes, but this is other scope.
Lets see how this functions is called and how text and size are supplied to figure out the string object.
EBX helds the string object and there are two pointers, a pointer to the string on 0x18 and the length in 0x18, lets verify it on windbg.
And here we have the string object, 0x0000001e is the length, and 0x001de8a68 is the pointer.
Thanks @capi_x for the pascal samples.
Related word
- Hacking Pages
- Hacking Madrid
- Hacking Background
- Curso Hacking Etico
- Hacking Quotes
- Hacking Tutorials
- Growth Hacking Pdf
- Hacking Traduccion
- Pagina Hacker
- Hacking Movies
- Hacking Web Sql Injection